Encrypted Calls with End-to-End Security: The Gold Standard for Private Communication
-
February 3, 2022
-
7 min read

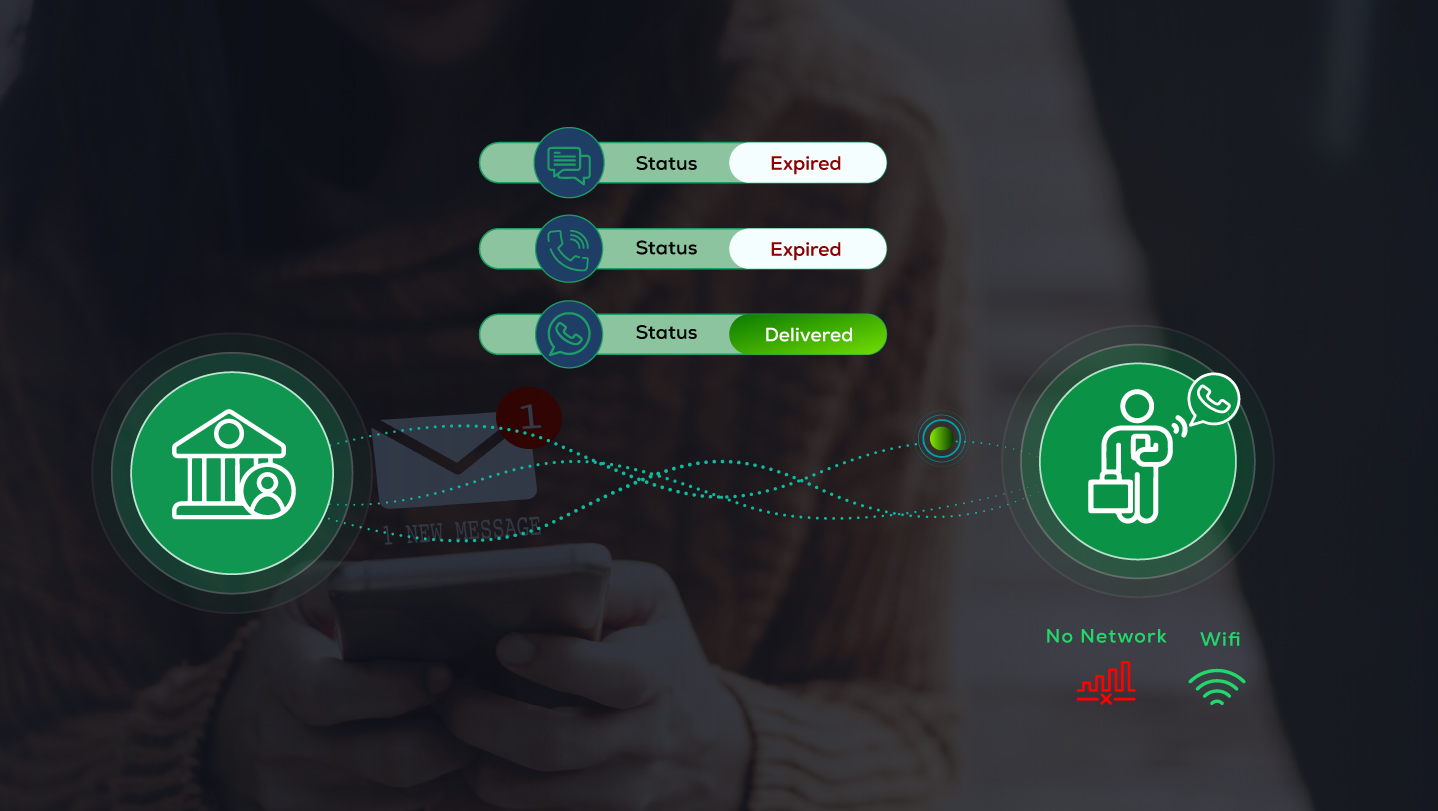
E2EE is a secure communication method that ensures the safety and confidentiality of encrypted phone calls until it is delivered to the intended receiver.
Widely recognized for its advanced security level, E2EE is now implemented by several popular platforms, including Signal, WhatsApp, and even Snapchat. This comprehensive security solution has emerged as a gold standard for private communication. E2EE offers end-to-end security and privacy of communication content when shared over the Internet. This safety barrier blocks third parties or hackers from accessing your content and data even if the communication medium is compromised.
But what does this end-to-end encryption mean? How does encrypted VoIP work? In this article, we’ll be discussing everything from the significance, and benefits of encrypted calls to the vulnerabilities of End to End Encrypted communication.
Let’s dig a little deeper to gain some valuable E2EE details!
Safeguarding Privacy in Communication
E2EE has emerged as a powerful security tool that safeguards our private communication or data shared on digital platforms. The E2EE concept goes beyond safety measures. It creates a secret channel for a specific sender and receiver. It is so secure that even the encrypted cell phone service provider can’t decipher or snoop into your content. No intended user can access the confidential data exchanged between two parties. Unlike legacy encryption practices, E2EE protects your data in transit and on the server.
It uses public and private cryptographic keys to secure phone calls and data. Using cryptographic algorithms, it scrambles the conversation between both parties into illegible text, making it impossible for unauthorized third parties or hackers to access private conversations. E2EE promises to keep individual or business communications private and safe.
Understanding End-to-End Encryption: A Primer
E2EE can be better described as a double-lock software security solution that uses a ‘key’ to encrypt a message on the receiver end or decrypt the message on the sender’s end. Here, ‘Key’ refers to the mathematical algorithm that is used to secure phone calls. E2EE relies on two types of asymmetric cryptographic Keys:
- Public Key is used when encoding a message and is easily accessible to anyone during the transit period. With E2EE, messages cannot be encrypted or decrypted at any point during the transit of encrypted VoIP calls. Whereas,
- The Private Key ensures privacy and is used to decode a message. It is shared only with the intended sender, so even if the communication channel is compromised, your privacy is not violated.
Both the keys are interlinked through a secure mechanism called ‘public key cryptography.’ Public and private keys are temporary and disappear after the messages are shared successfully. Let’s understand how the concept of E2EE works.
Step 1: You text on WhatsApp, Snapchat, or any other encrypted phone call app.
Step 2: Now, the app uses the public key to encode or encrypt the message.
Note: The public Key alone cannot translate or decode the message when transferred over encrypted VoIP calls.
Step 3: The encrypted message is shared over the Internet.
Step 4: The intended sender requires the Private Key to decrypt the message.
Besides ensuring the safety and privacy of your text or data, the E2EE mechanism has also helped remote employees access the company’s confidential data and tools.
Importance of Secure Communication Channels
Can you trust any random person to deliver your confidential document to another location? Is it possible in the real world? No! The same logic applies to phone calls and data when transferred from one end to another. Check why it is important to use secure communication channels
- Encrypt sensitive data like financial documents, business details, medical reports, etc., to unreadable form.
- Maintains Compliance with set security standards and data regulation laws.
- It prevents prying eyes and identity thefts from accessing your emails, messages, and personal video messages.
- Helps personal relationships or business collaborations to foster trust and long-term relationships.
Exploring Encrypted Call Technologies
Symmetric Encryption
Such encryption technology relies on a single key shared between parties to encrypt and decrypt the data. A secure key exchange is required to prevent data breaches or disrupted business operations.
Asymmetric Encryption
As discussed in this guide, E2EE is based on asymmetric encryption. It uses a pair of public keys for message encryption and a private key for decryption at the receiver’s end.
Signal Protocol
This technology is the perfect combination of symmetric and asymmetric encryption. Popular messaging platforms like WhatsApp and Signal use this highly efficient open-source protocol.
SRTP
Secure Real-time Transport Protocol (SRTP) encrypts voice, video messages, and VoIP calls. It also provides high-end security for signalling data.
Benefits of End-to-End Security in Private Communication
Encrypted phone calls maintain the privacy and security of users’ sensitive or insensitive information. Now, let’s examine several significant benefits of Encrypted Phone calls with E2EE security.
Prevents Unauthorized Access
Hackers or Identity thieves can’t decrypt your confidential data in transit. The unreadable script can be decoded only at the receiver’s end using the private key. So, sharing any financial or private data over encrypted platforms is completely safe.
Discourages Tampering
E2EE scrambles the conversation at the sender’s end using an algorithm to maintain the integrity of data or calls. There is no way for unauthorized third parties to tamper, damage, or alter your content with negative intent.
No snooping by Service Providers
The best part about E2EE is that the private key is stored only in the user’s device. This means the encrypted cell phone service doesn’t have access to the data exchanged between the sender and the receiver.
Trust and Transparency
E2EE’s transparent methodology helps build confidence and long-term customer relationships. It allows businesses to discuss confidential matters over the phone without fear of data leakage.
Challenges and Considerations in Implementing Encrypted Calls
Amidst the various security features, E2EE still needs to be a complete security solution. Though it encrypts your data (audio, video, screen sharing) and content while communicating through apps, it could be more effective in terms of metadata. Put, hackers can’t identify what the data is, they can still identify:
- Who is the sender and receiver? and
- When were the messages shared?
It doesn’t give the authority to encrypted phone calls app owners like WhatsApp, Zoom, etc., to monitor illegal or irrelevant data sharing between the two parties. Even they can’t listen to or read your content. It prevents messaging platforms from offering automated or AI-generated features like
- Contextual services
- Live captions
- Transcriptions
- Calendar invites
- Message history, etc.
Apart from these facts, E2EE can also be vulnerable if someone on either of the ends has unauthorized access to your device.
Comparing Encrypted Call Solutions: Which One Fits Your Needs?
Whatsapp, Viber, Telegram, and Signal are some of the widely used encrypted call solutions. However, it is essential to identify your data and security requirements. To choose the best encryption platform that fits your needs, you need to check whether or not the encryption solution offers
- On-premises Data encryption
- Encryption key policies and configuration
- Automated lifecycle for encryption keys
- Regular Audits
- Role-based access controls
- Centralized managed dashboard
Steps to Ensure Secure Communication Practices
- Secure your device with a strong and unique password.
- Regularly update the device software to add an extra layer of security.
- Never click the malicious links sent through SMS, email, or pop-ups.
- Install reputed anti-malware software to detect phishing attacks or malware.
- Don’t use public Wi-Fi to share confidential data.
- Keep yourself updated and informed about cyber threats and security practices.
Conclusion: Embracing Privacy in Every Call
Undeniable, Encrypted phone calls with E2EE stand as the gold standard for securing private communication. E2EE is a powerful layer of security that prevents data from service providers, phishing attacks, and eavesdroppers. However, Robust security practices at the sender and receiver ends are essential to keep the potential threats at the edge. In a nutshell, E2EE is a well-rounded approach for businesses and individuals to maintain data integrity and privacy in modern workspace.
Upgrade communication with Airtel Business’ Cloud Telephony solutions. Explore our programmable voice solutions that easily combine high-quality calling with dependable and secure communication.
 Share
Share